Windows Phone
Microsoft’s range of Windows Phone devices suffers from a denial-of-service attack that allows attackers to disable the messaging functionality on a device. The flaw in Windows Phone, which affects the latest build of Windows Phone 7.5 Mango, as well as previous versions regardless of the manufacturer or model. It was first discovered by Windows Phone hacker Khaled Salameh. Rather than following in the tradition of hackers, he worked with the site WinRumors to report the bug and securely disclose it to Microsoft.
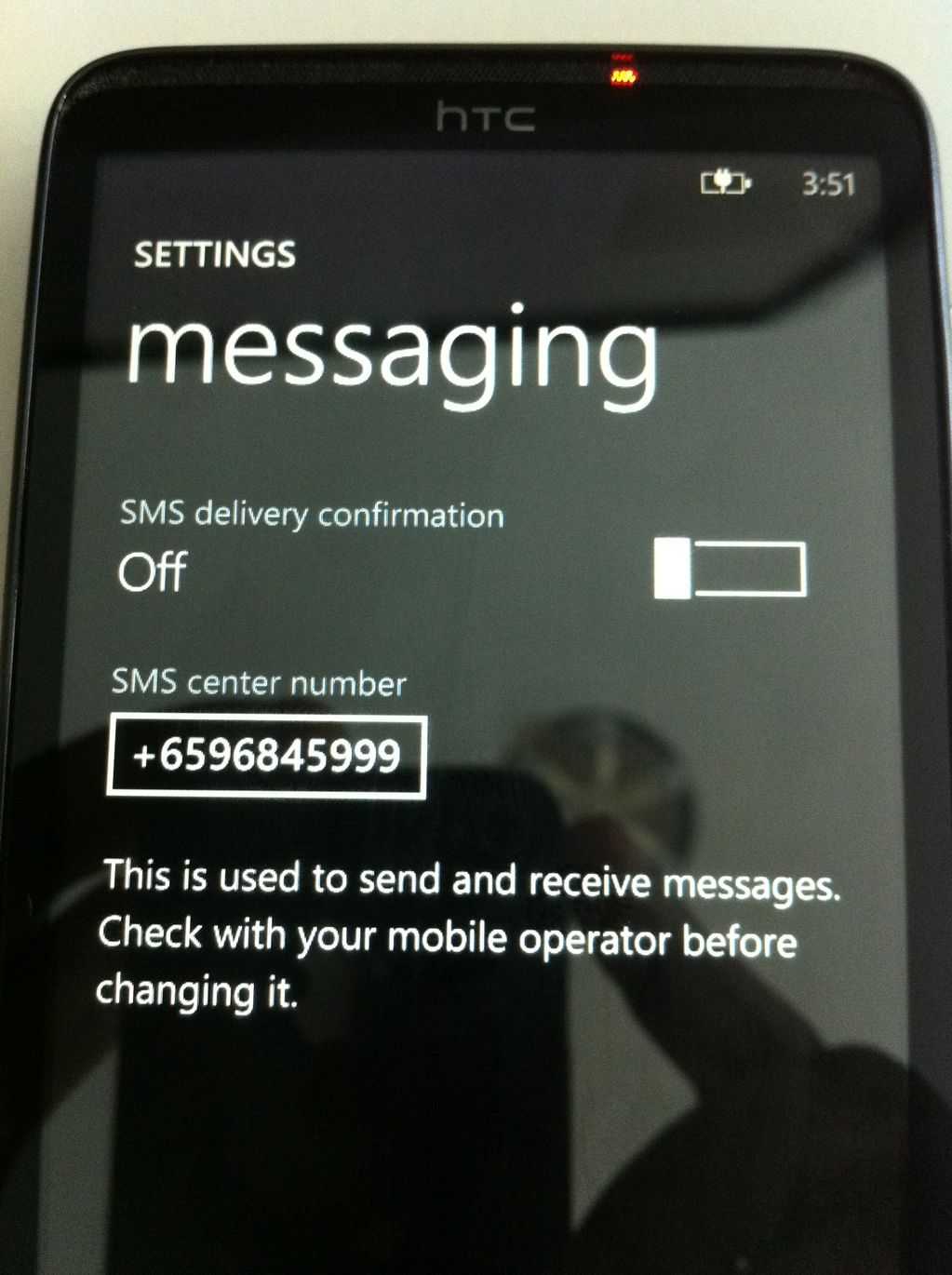
The attack works by sending a message to the Windows Phone message hub application. As this app accepts a variety of messages, the attacking message can be in the form of an SMS text message, a Facebook message, or a Windows Live Messenger hub. The flaw appears to affect other aspects of the Windows Phone operating system too. When the message is received, errors in the handling in the hub cause the message to lock the device, killing whatever work you had in the process. You can recover via a reboot.
However, your message hub app will stay dead. It is unclear if there is a fix for restoring messaging functionality, but barring a reformat of your device, the affected phone may be unable to message. Worse yet, if you have a live tile from the contact that sent the message, once it updates post-reboot it will trigger another system lock-up. There is a workaround for this: quickly navigate to the home screen and remove/unpin the tile before it “flips” (updates).
Here’s a video, courtesy of WinRumors of the attack in action:
For now, as mentioned, this severe vulnerability’s implementation details are under wraps, pending a fix, so Windows Phone users should only be mildly concerned.
Again, this vulnerability appears to be solely capable of denial of service and does not affect your system security. Both Apple and Google have suffered from SMS bugs with their iOS and Android devices as discovered by researchers Collin Mulliner, a Ph.D. student in the Security in Telecommunications department at the Technische Universitaet Berlin, and Nico Golde, an undergraduate student at the same institution.
These attacks differ from security-breach attacks, like the SMS attack that affected older unpatched versions of iOS, first discovered by Charlie Miller that allowed attackers to complete control over an iPhone at the time.
The key difference is that those kinds of attacks utilize flaws in messaging apps that allow the execution of arbitrary code as a path to root control; whereas attacks like the one in this article exploit flaws in message handling which do not execute arbitrary code, but do trigger some sort of catastrophic system failure.
